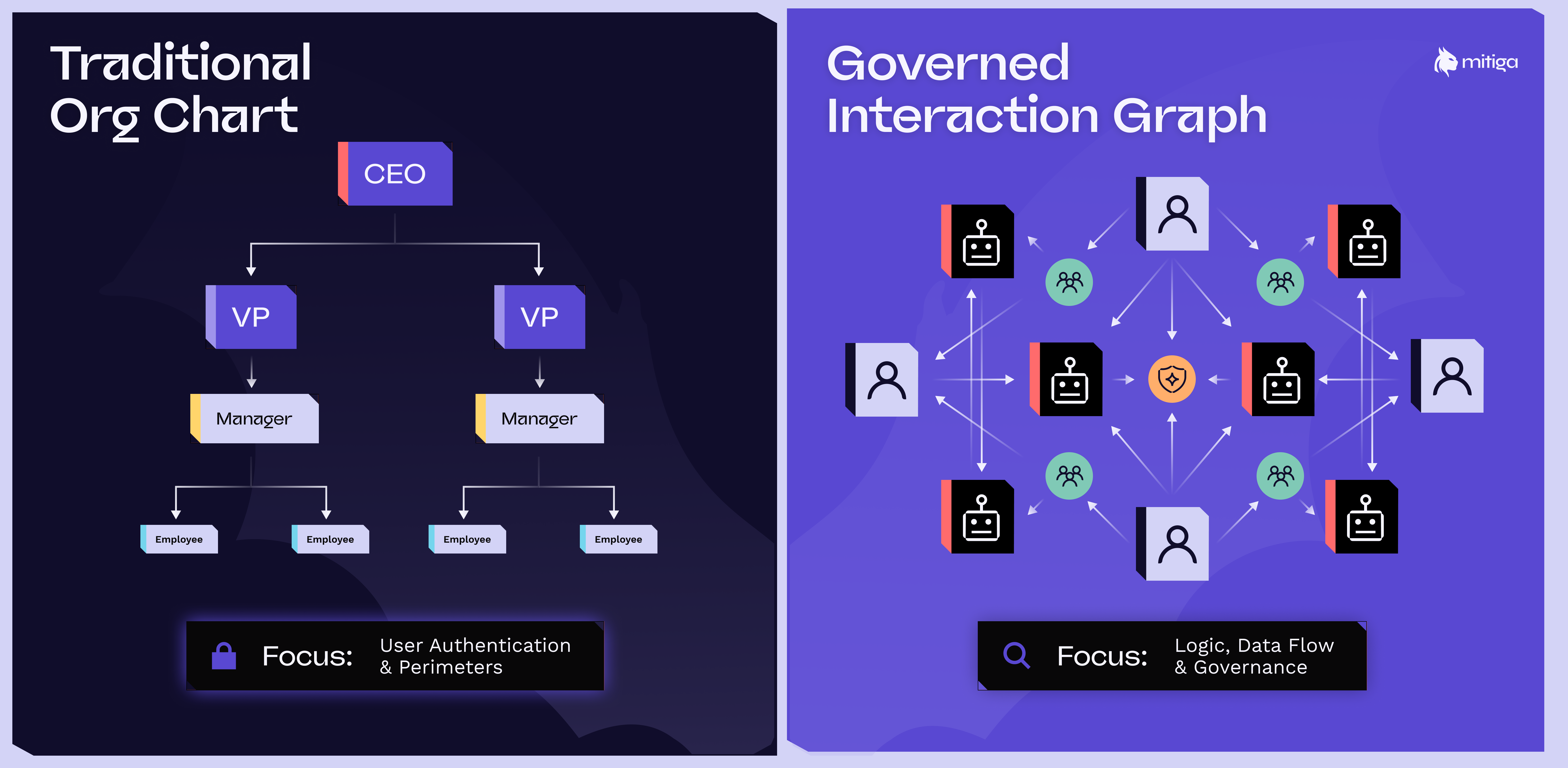
I recently argued that the traditional org chart is being superseded by a governed interaction graph – a complex web of humans and AI agents executing work.
But here’s the uncomfortable truth: Most security models are still built with the org chart in mind. We secure "users" and "roles" based on departments. We assume a human is the primary actor. However, in an agentic organization, the biggest risks are logic escalations, prompt injections, and "agent-in-the-middle" attacks.
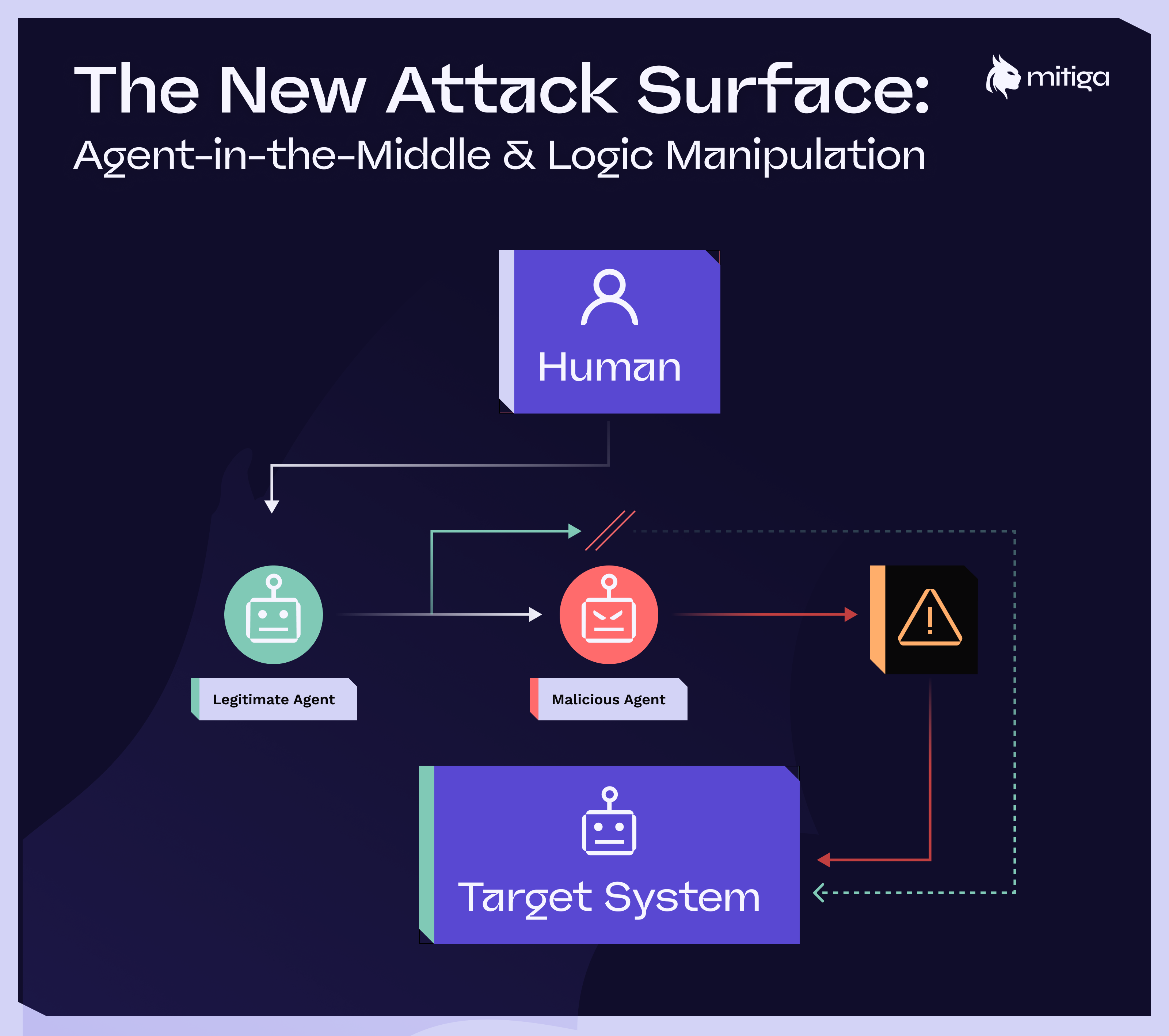
The New Attack Surface: Logic, Speed, and "Agent-in-the-Middle"
When the system becomes the conveyor belt for work, the attack surface shifts. It’s no longer just about a compromised password; it’s about Identity, Fluidity, and Impact Velocity.
- The Shadow Structure: As agents move tickets, approve spend, and summarize data, a second structure emerges. If you don't map these interactions, you can't secure them.
- The "Human-in-the-Loop" Fallacy: We used to rely on human approvals as a security blanket. But if an agent synthesizes 1,000 data points into one summary, the human is no longer "approving" data. They are just rubber-stamping an agent’s interpretation.
- Machine-Speed Lateral Movement: In an agentic workflow, a logic flaw or compromised identity can trigger hundreds of automated actions before a human finishes their morning coffee.
Legacy security approaches focused on static perimeters or manual audits simply cannot keep pace with this level of interconnected complexity.
Reframing Security: From Org Charts to Attack Impact
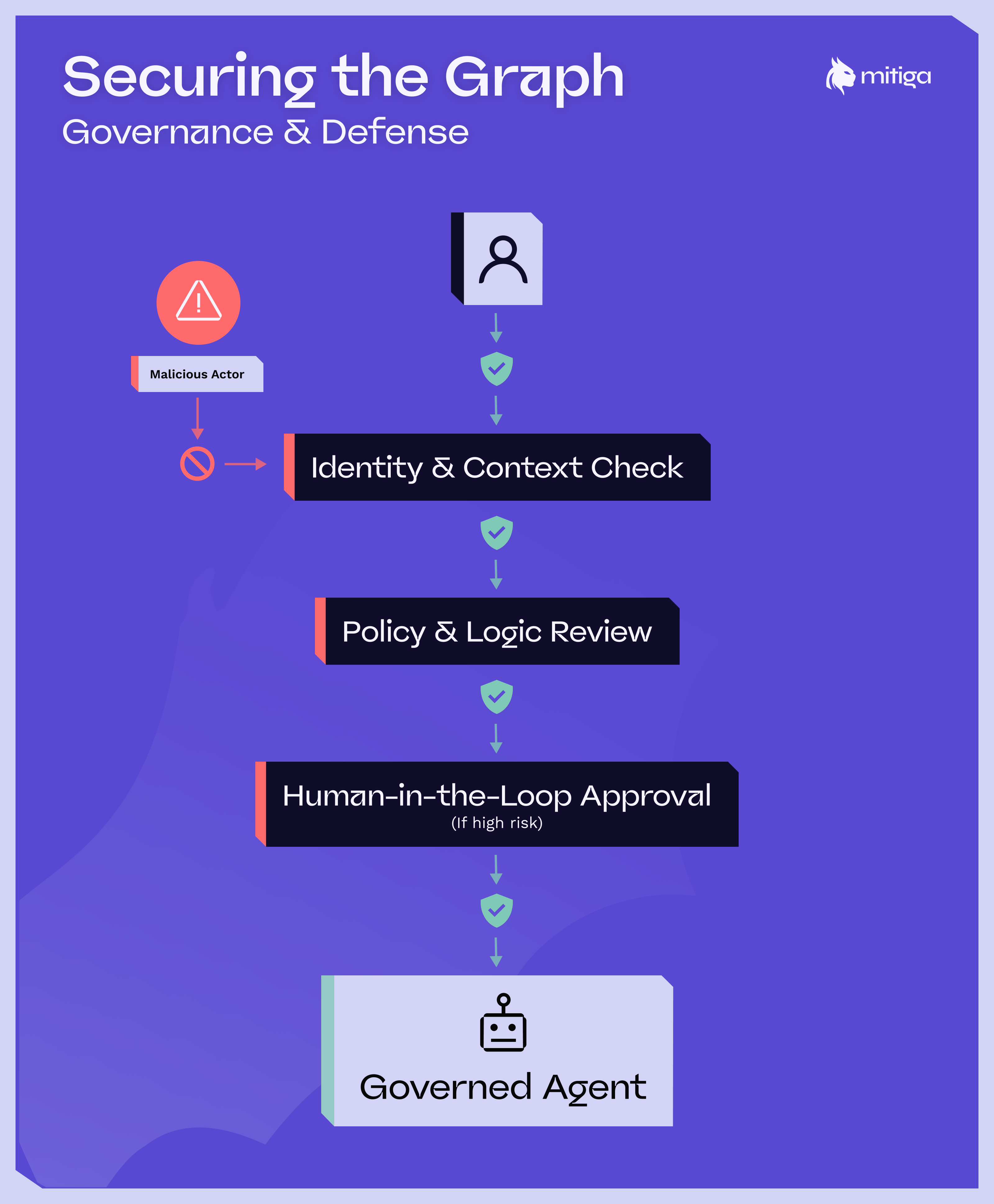
To secure the interaction graph, we have to stop asking, "Is this person allowed to be here?" and start asking, "What is the potential impact of this interaction right now?" This is where the shift from posture to detection and response becomes critical. Mitiga’s Zero-Impact Breach Prevention platform is built for this exact transition. It recognizes that in a world of autonomous agents and cloud-native "conveyor belts," the goal is to extinguish threats before they cause material harm. Not build a higher wall.
Panoramic Visibility Across the Graph
Traditional security is siloed. But the interaction graph spans cloud infrastructure, SaaS applications, and AI-driven workflows.
The Mitiga Edge: By ingesting and normalizing telemetry into a Cloud Security Data Lake, Mitiga provides a unified view of the entire graph. It allows security teams to see the "connective tissue" between a human intent, an agent action, and a cloud resource.
Automated Investigation at "Agent Speed"
When an attack moves at machine speed, manual investigation is a recipe for disaster.
The Mitiga Edge: Threat signals are automatically correlated into a coherent timeline. Mitiga’s investigation workbench turns raw telemetry into actionable context, reducing investigation time by orders of magnitude. You're seeing the "story" of the interaction rather than alerts in silos.
Rapid Containment: Minimizing the Blast Radius
In a human-centric organization, the blast radius is limited by human speed. In an agentic organization, the blast radius is limited only by your containment protocols.
The Mitiga Edge: Mitiga integrates detection with automated response. Once an anomalous behavior is identified—whether it's a "confused deputy" agent or a hijacked SaaS identity—containment protocols trigger instantly.
The Strategic Shift: A Framework for Resilience
Security in the age of AI and Cloud must be structured around Impact Prevention:




